中文说明详见https://www.oheng.com/tips/280
After you determine the pattern for the account lockouts and narrow down your scope to a specific client computer or member server, you should gather detailed information about all of the programs and services that are running on that computer. Some of the information that you should obtain includes:
- Mapped network drives
- Logon scripts that map network drives
- RunAs shortcuts
- Accounts that are used for service account logons
- Processes on the client computers
- Programs that may pass user credentials to a centralized network program or middle-tier application layer
The following sections discuss the tools that you can use to help you gather information from the network environment.
The LockoutStatus.exe Tool
The LockoutStatus.exe displays information about a locked out account. It does this by gathering account lockout-specific information from Active Directory. The following list describes the different information that is displayed by the tool:
- DC Name: Displays all domain controllers that are in the domain.
- Site: Displays the sites in which the domain controllers reside.
- UserState: Displays the status of the user and whether that user is locked out of their account.
- Bad Pwd Count: Displays the number of bad logon attempts on each domain controller. This value confirms the .domain controllers that were involved in the account lockout.
- Last Bad Pwd: Displays the time of the last logon attempt that used a bad password.
- Pwd Last Set: Displays the value of the last good password or when the computer was last unlocked.
- Lockout Time: Displays the time when the account was locked out.
- Orig Lock: Displays the domain controller that locked the account (the domain controller that made the originating write to the LockoutTime attribute for that user).
Where to Obtain the LockoutStatus.exe Tool
LockoutStatus.exe is included with the ALTools.exe package that is available at “Account Lockout and Management Tools” on the Microsoft Web site.
How to Install the LockoutStatus.exe Tool
To install the LockoutStatus.exe tool, install the ALTools package on your domain controller.
How to Use the LockoutStatus.exe Tool
To run the LockoutStatus.exe tool and display information about a locked out user account:
- Double-click LockoutStatus.exe.
- On the File menu, click Select target.
- Type the user name whose lockout status on the enterprise’s domain controllers you want information about.
The following figure displays an example where two domain controllers have a badPwdCount value of 5, which is also the bad password threshold. One domain controller is the PDC operations master, and the other domain controller is the authenticating domain controller. These two domain controllers are displayed because of password chaining from the authenticating domain controller to the PDC.
Figure 2: The LockoutStatus.exe Tool
.gif)
The ALockout.dll Tool
The ALockout.dll tool and the Appinit.reg script are included in the ALTools package. ALockout.dll is a logging tool that may help you determine the program or process that is sending the incorrect credentials in an account lockout scenario. The tool attaches itself to a variety of function calls that a process might use for authentication. The tool then saves information about the program or process that is making those calls into the Systemroot\Debug\Alockout.txt file. The events are time stamped so that you can match them to the events that are logged in either the Netlogon log files or the Security event log files.
You can use Appinit.reg to initialize the .dll file. This file provides no other functionality.
Note:
Microsoft does not recommend that you use this tool on servers that host network programs or services. You should not enable ALockout.dll on Exchange servers because the ALockout.dll tool may prevent the Exchange store from starting.
Important:
Before you install the ALockout.dll tool on any mission-critical computer, make a full backup copy of the operating system and any valuable data.
For more information, see “Errors Installing Exchange Server with CleanSweep” on the Microsoft Knowledge Base .
In most account lockout scenarios, you should install ALockout.dll on client computers. Use the information that is stored in both the Netlogon log file and the Security event log to determine the computers from which the incorrect credentials are being sent that are locking out the user’s account. When you install the ALockout.dll tool on the client computer that is sending the incorrect credentials, the tool logs the process that is sending the incorrect credentials.
Where to Obtain the ALockout.dll Tool
ALockout.dll is included with the ALTools.exe package that is available at “Account Lockout and Management Tools” on the Microsoft Web site .
How to Install the ALockout.dll Tool
There two versions of the ALockout.dll file. One version of the file is for computers that are running a Windows 2000 operating system, and the other version of the file is for computers that are running a Windows XP operating system. View the Readme.txt file that is included with the ALTools package.
To install ALockout.dll
- On the computer that has generated account lockout error messages in the Security event log, copy both the ALockout.dll and Appinit.reg files to the Systemroot\System32 folder .
- Double-click the Appinit.reg file to run the script. When you do this, the ALockout.dll file is registered and can begin providing information.
- Restart the computer to complete the installation.
How to Remove the ALockout Tool
To remove the ALockout.dll file from the computer
- At a command prompt, type regsvr32 /u alockout.dll.
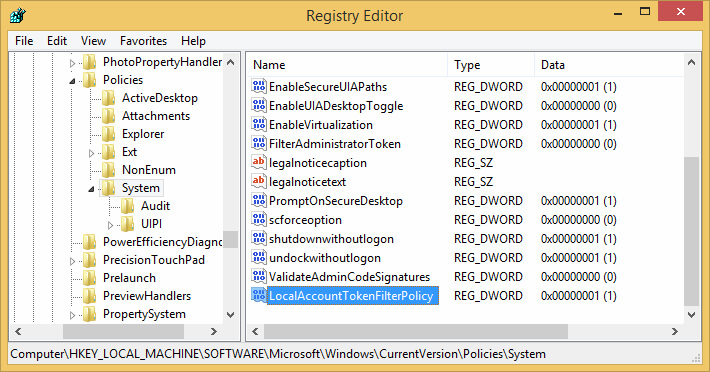
- Delete the Alockout.dll value that is under the following registry key:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\
Windows AppInit_DLLs
After you delete the Alockout.dll value, the AppInit_DLLs registry key is blank. - Restart the computer.
- Delete the ALockout.dll file from the Systemroot/System32 folder.
How to Use the ALockout.dll Tool
You should use the ALockout.dll tool with Netlogon logging and security auditing. To use the ALockout.dll tool:
- Wait for an account to lock out on the computer.
- When an account is locked out, the ALockout.txt file is created in the Systemroot\Debug folder.
- Compare event time stamps in ALockout.txt with the time stamps in both the Netlogon log files and the Security event log files. When you do this, you can determine the process that is causing the lockouts.
You can use the ALockout.dll tool if you have already set up Netlogon logging, as well as Kerberos and logon auditing on the local computer. ALockout.dll does not interfere with any other logging or event generation.
The ALoInfo.exe Tool
If account lockouts seem to happen most frequently after a user is forced to change their password, you may want to determine which users’ passwords are about to expire. You can use the ALoInfo.exe tool to display all user account names and the password age for those user accounts. This will allow you to use the ALockout.dll tool and other account lockout tools to set up the tools prior to the initial account lockout. You can also obtain a list of all local services and startup account information by using the ALoInfo.exe tool.
Note:
You can also use the SecDump tool to display password expiration information in a Windows NT Server 4.0 domain. You can download this tool from the SystemTools Web site . Note that Web addresses can change, so you might be unable to connect to the Web site or sites mentioned here.
Where to Obtain the ALoInfo.exe Tool
The ALoInfo.exe file is included with the ALTools.exe package that is available at “Account Lockout and Management Tools” on the Microsoft Web site .
How to Install the ALoInfo.exe Tool
To install the ALoInfo.exe tool, install the ALTools package on your domain controller. The ALTools package contains the ALoInfo.exe tool.
How to Use the ALoInfo.exe Tool
You can use ALoInfo.exe at a command prompt with either of the following methods:
•To display an accounts password ages from a domain controller, at a command prompt, type the following:
aloinfo /expires /server:Domain_Controller_Name
•To display all local service startup account information and mapped drive information for a user who is currently logged on, at a command prompt, type the following command:
aloinfo /stored /server:Computer_Name
You can redirect the output of ALoInfo.exe to a text file and then sort the results to determine which users may be involved in the account lockout. This information can also be stored for later analysis.
The AcctInfo.dll Tool
You can use the AcctInfo.dll tool to add new property pages to user objects in the Active Directory Users and Computers MMC Snap-in. You can use these property pages to help isolate and troubleshoot account lockouts and to reset a users password on a domain controller in that user’s local site.
AcctInfo.dll displays the following user account information that you may be able to use to identify and resolve account lockout issues:
- Last time the password was set
- When the password will expire
- User Account Control Raw Value and Decode
- Time the account was locked out
- If the account is locked out now, when it will be unlocked
- Security identifier (SID) of the account, and its SIDHistory
- Globally unique identifier (GUID) of the account
- These account properties:
- Last Logon
- Last Logoff
- Last Bad Logon Time
- Logon Count
- Bad Password Count
You can also use the AcctInfo.dll tool to obtain the domain password information (expiration, lockout time, and so on). You can type the user’s computer name in the tool, and then reset the user’s password on a domain controller in that user’s site.
Note:
Because of replication latency, domain controllers may store different information about the same user account. AcctInfo.dll displays information that is retrieved from a single domain controller.
Where to Obtain the AcctInfo.dll Tool
The AcctInfo.dll tool is included in the ALTools.exe package that is available at “Account Lockout and Management Tools” on the Microsoft Web site .
How to Install the AcctInfo.dll Tool
On the computer where you want to run Active Directory Users and Computers MMC Snap-in:
- Copy the AcctInfo.dll file to the System32 folder.
- At a command prompt, type regsvr32 acctinfo.dll, and then press ENTER.
The AcctInfo.dll file is registered and is displayed on a user’s property sheet in the Active Directory Users and Computers MMC Snap-in after you follow these steps.
To use the Account Lockout Status button in the tool, verify that LockoutStatus.exe is in the Systemroot\System32 folder. If LockoutStatus.exe is not installed in this location, this button is unavailable.
How to Use the AcctInfo.dll Tool
To use the AcctInfo.dll tool, open the Active Directory Users and Computers MMC, right-click a user, click Properties, and then click Additional Account Info. An example of the information that is provided by AcctInfo.dll is shown in the following figure.
Figure 3: Main Property Box
The following figure displays the domain password policy information that you can view to determine the password policy that applies to the domain controller.
Figure 4: Domain Password Policy
Change Password on a Domain Controller in the User’s Site
The AcctInfo.dll tool allows you to increase the functionality of the Active Directory Users and Computers MMC by adding the ability to reset a user’s password in that user’s local site. When you reset the password in the remote site, you avoid replication delays that can occur before that user logs on.
When you reset the password, you can also unlock the account and set the User must change password value. These options are in the Change Password On a DC In The Users Site box as displayed in the following figure.
Figure 5: Change Password On a DC In The Users Site
How to Remove the AcctInfo.dll Tool
To remove the AcctInfo.dll tool, delete the AcctInfo.dll file from the Systemroot/System32 folder, and then type the following command at a command prompt:
regsvr32 /u acctinfo.dll
The EventCombMT.exe Tool
You can use the EventCombMT.exe tool to gather specific events from event logs from several different computers into one central location. You can configure EventCombMT.exe to search for events and computers. Some specific search categories are built into the tool, such as account lockouts. Note that the account lockouts category is preconfigured to include events 529, 644, 675, 676, and 681.
Figure 6: The EventCombMT.exe Tool
Where to Obtain the EventCombMT.exe Tool
The EventCombMT.exe tool is included in the ALTools.exe package that is available at “Account Lockout and Management Tools” on the Microsoft Web site .
How to Install the EventCombMT.exe Tool
You do not need to install this tool separately. When you install ALTools on the domain controller, EventCombMT.exe is also installed to the directory you specified during setup.
How to Use the EventCombMT.exe Tool
To use the EventCombMT.exe tool, open the folder you specified during setup for ALTools, double-click EventCombMT.exe, click the Searches menu, click Built in searches, and then click Account lockouts. When you do this, the events that will be pulled from the event logs are automatically displayed in the tool. These events are from all of the domain controllers in your environment. In addition to 529, 644, 675, and 681, type 12294 in the Event Ids box, and then click Search. The tool then searches the computers for these events, and then saves them to a .txt file that you specify.
The NLParse.exe Tool
Because Netlogon log files may become more than 10 MB in size, you may want to parse the files for the information that you want to view. You can use the NLParse.exe tool to parse Netlogon log files for specific Netlogon return status codes. The output from this tool is saved to a comma-separated values (.csv) file that you can open in Excel to sort further.
Note:
The return codes that are specific to account lockouts are 0xC000006A and 0xC0000234.
The following figure displays the interface for the NLParse.exe tool.
Figure 7: Netlogon-Parse Return Status Codes
Where to Obtain the NLParse.exe Tool
The NLParse.exe tool is included in the ALTools.exe package that is available at “Account Lockout and Management Tools” on the Microsoft Web site .
How to Install the NLParse.exe Tool
You do not need to install this tool separately; when you install ALTools on the domain controller, NLParse.exe is also installed.
How to Use the NLParse.exe Tool
To use the NLParse.exe tool, open the folder you specified during setup for ALTools, double-click Nlparse.exe, click Open to open the Netlogon.log file that you want to parse, select the check boxes for the status codes that you want to search for, and then click Extract. After you do this, view the output from the NLParse.exe tool. Typically, you may want to look at both the 0xC000006A and 0xC0000234 code statuses to determine from where the lockouts are coming.
The FindStr.exe Tool
You can also use the FindStr.exe tool to parse Netlogon log files. FindStr.exe is a command-line tool that you can use to parse several Netlogon.log files at the same time. After you gather the Netlogon.log files from several domain controllers, extract information about a specific user account from the files (user1, error code 0xC000006A, or error code0xC0000234). You can use this tool to help you obtain output about a user, computer, or error code in the Netlogon.log files.
Where to Obtain the FindStr.exe Tool
The FindStr.exe tool is included in the default installation of Windows 2000, Windows XP, and the Windows Server 2003 family operating systems. No additional installation or configuration is required for the FindStr.exe tool.
How to Use the FindStr.exe Tool
To use the FindStr.exe tool, rename the Netlogon.log files, and then save the files to one folder. To parse all of the Netlogon log files, type the following command at a command prompt:
FindStr /I User1 *netlogon*.log >c:\user1.txt







Email –
comments – I am really happy with your blog because your article is very unique and powerful for new reader.
Thanks!
Have you ever heard of a problem where the Lotus Connection web based feed client tries to authenticate to a sharepoint feed using LC credentials?
I’m trying to find out how LC handles authenticated SP blogs. If it in fact tries to repeatedly authenticate with Lotus Connection credentials that would have caused my lockout scenario.
I’ve been suffering from recurrent account lockouts that our IT group has been unable to diagnose.
Are there any XP client programs I can install on my own machine to inspect all authentication issues? I could then, at least to my own satisfaction, determine if my machine was really making the authentication requests and, if it was, figure out the source.
I’ve subscribed to the comment feed here if you can reply in comments. Or you can use the email address I’ve provided here if you’d like.
Very much appreciated!
Thanks!
AcctInfo.dll can be installed on client side to log bad password. but I have to say it’s not helpful at most of time. bad password may come from other source.
So I still suggest you to contact IT group to find clue from server side. also you can check if some services is started up by your account via services.msc command